According to reports, the hacker group Lapsus $ first released a screenshot of C / C + + instructions in Samsung software before releasing the leaked content, claiming it contained confidential source code from Samsung.
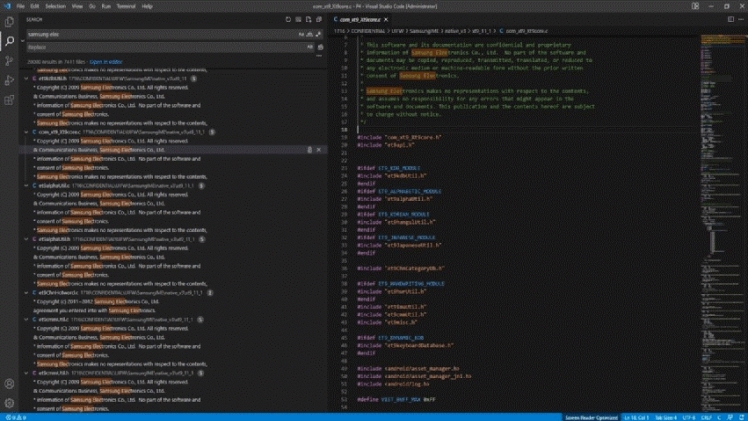
According to the hacker organization, the leaked data includes: the source code of each trusted applet (TA) installed in the Samsung TrustZone environment for sensitive operations (such as hardware encryption, binary encryption, and access control), all biometric unlocking device algorithms, the source code of all the latest Samsung devices’ boot loaders, and the source code of the Samsung activation server. Complete source code (including API and services) of the technology used to authorize and verify Samsung accounts, confidential Qualcomm source code, and so on.
Furthermore, the hacker group Lapsus $ has divided the data into three compressed files, with a total file size of nearly 190GB, and has opened external download channels. The organization also stated that it would increase the number of servers deployed to improve download speeds. After the news broke, many in the industry expressed concern that if the information is correct, it indicates that Samsung has experienced a major data leak, which could cause significant damage to the company.
It is understood that obtaining the source code allows hackers to discover vulnerabilities in the device security system, exposing users to the risk of data theft.
According to the verge report, Samsung Electronics issued a statement on March 7 to confirm the data leak, but denied that it would affect customers’ or employees’ personal data.
According to Samsung, the company was recently informed of security vulnerabilities related to internal data. The security system was immediately strengthened after the incident was discovered. According to the preliminary analysis of the company, the disclosure includes some source code related to the operation of Galaxy devices but does not include any personal information of consumers or employees.
“At the moment, the company does not anticipate any impact on business or customers. It has taken precautions to avoid similar incidents in the future and will continue to provide services to customers.” According to Samsung.
According to reports, Lapsus $ is a highly confidential hacker organization. It previously attacked the Brazilian Ministry of Health’s network system and hacked the official websites of a newspaper and a TV channel owned by the impresa group, Portugal’s largest media conglomerate. The hacker organization did not mention the ransom issue in relation to Samsung’s data disclosure, nor did it say it would communicate with Samsung.
It is worth noting that the international chip giant NVIDIA was recently targeted by the hacker organization.
Lapsus $ publicly admitted at the end of February this year that it had carried out a cyber attack on NVIDIA and had approximately 1 TB of data from NVIDIA. The hardware folder alone is 250GB in size, and it contains information about “all recent NVIDIA GPUs,” among other things.
Vinchin Backup & Recovery is the world’s most easy-to-use, flexible and reliable VM backup tool, which supports most of the virtualization environments. Vinchin supports the world’s most mainstream virtual environments including VMware, XenServer/XCP-ng, Hyper-V, RHV/oVirt, OpenStack, Sangfor HCI, Oracle Linux Virtualization Manager and Huawei FusionCompute(Xen Based). It prevents the loss of critical business data due to human misoperation, viruses, attacks, hardware failures, natural disasters, wars, etc. It now supports Chinese, English, German, Czech, etc. languages. By utilizing oVirt automatic backup, instant VM recovery and granular restore features, you can fully ensure the high recoverability of your critical data in oVirt VMs and absolute business continuity.